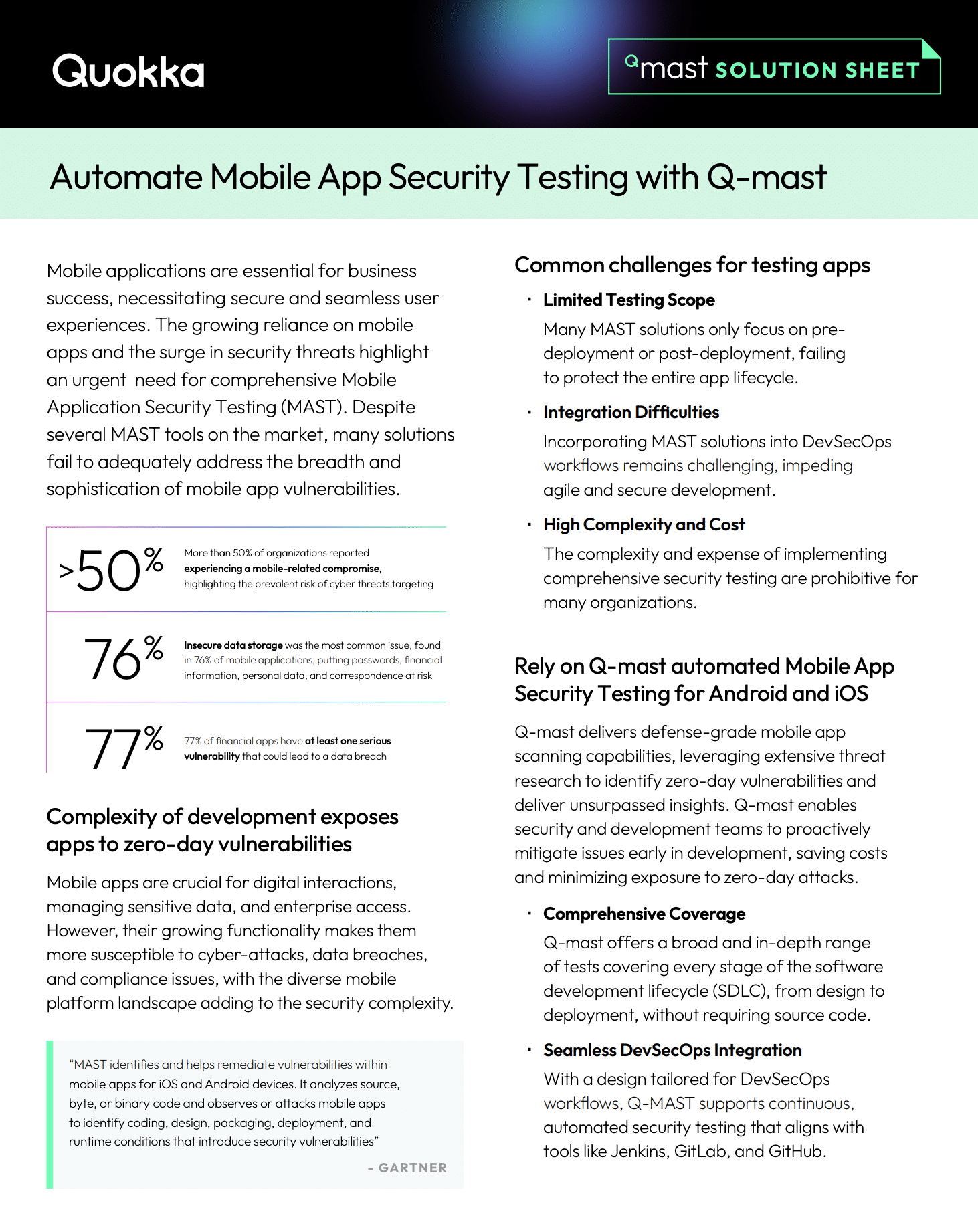
Q-mast: Comprehensive Mobile App Security Testing
- Solution Brief
Ensure your mobile apps are secure before deployment. Q-mast delivers in-depth security assessments to detect vulnerabilities, misconfigurations, and compliance risks. Download now to see how it fortifies mobile applications.
Our award-winning mobile app security technology

Mobile security that makes you smile.
Sign up for our newsletter, The Quokka Intel Briefing
Copyright © 2025, Quokka. All rights reserved.